Private Key vs Public Key: Understanding The Two & Their Importance In Crypto
Using cryptocurrencies is great.
But if you know a bit more about their basic cryptography, then it is best.
The basic underlying cryptography that forms the bedrock of cryptocurrencies is the public key and private key cryptography.
And many think that these are the same thing, but they are not.
That’s why today I am going to share with you the difference between a public key and private key, but before that, we need to talk about two different forms of encryptions, i.e., Symmetric Encryption and Asymmetric Encryption.
So let’s get the ball rolling:
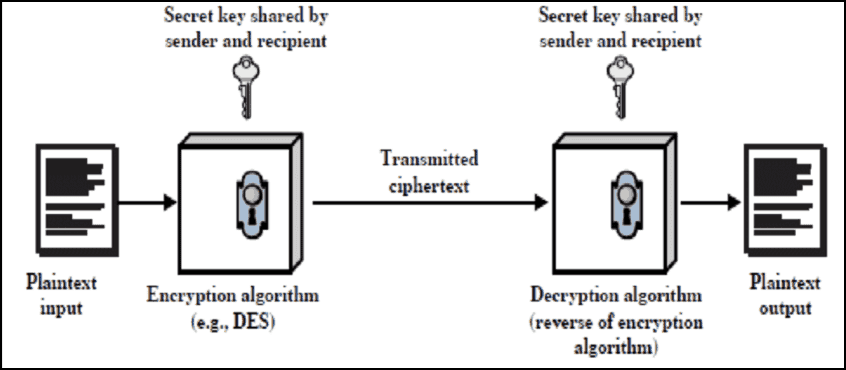
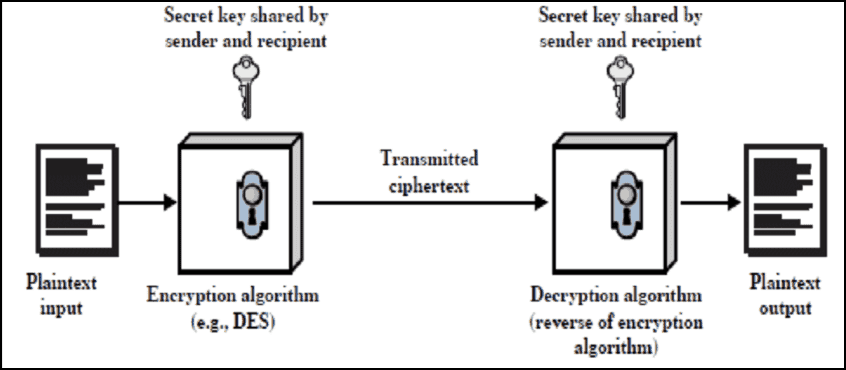
Symmetric Encryption
Symmetric encryption, it is solely based on one key, i.e., private key, which from its name is evident that needs to be kept private or secret.
A private key is just a number or alphanumeric string that is used to encrypt the underlying message or information.
Thus because of its nature, private keys need to be shared between two people if they want to read the underlying encrypted message.
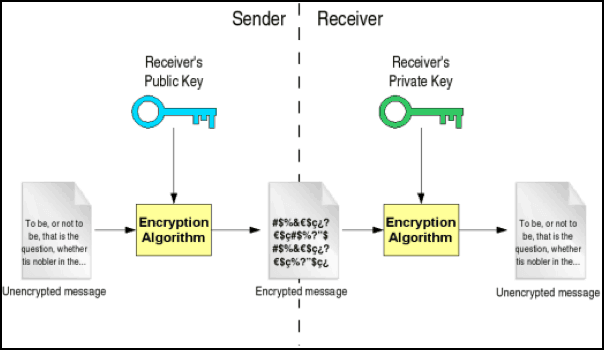
Asymmetric Encryption
Whereas in asymmetric encryption there are two keys which are used to communicate and these keys are known as a private key and public key.
This is also used to share messages between the two parties but without the need of sending another party, the private keys.
Hence this method is more secure because, in asymmetric key cryptography, the private key is kept by the sender and it usually takes a long time in encryption.
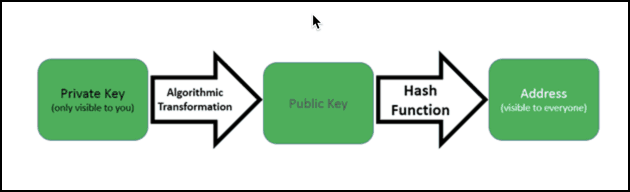
How Private key And Public Key Cryptography Works
Asymmetric cryptography uses private as well as the public key.
That’s why it is sometimes referred to as public-key cryptography also. But an important thing to understand about these two keys is this:
A public key is only used to encrypt the messages and cannot be used to decrypt those messages. That’s the reason public key stays public and can be given to anyone from whom you want to receive the message or a cryptocurrency transaction.
Whereas
A private key is intended to be private and is used to decrypt the messages encrypted with the linked public key.
Let say Bob wants to send Bitcoin transaction of 1 BTC to Alice:
Alice has its public key (A) and private key (B).
Now Alice shares her public key (A) to Bob.
Bob will use the public key (A) of Alice to encrypt the transaction of 1 BTC from Bob and send it across the channel.
Now Alice will decrypt this transaction using her Bitcoin private key (B) easily because public key (A) and private key (B) are interrelated mathematically.
And this is how messages or transactions move cryptographically in different blockchains generally with security and mathematical surety.
In respect of cryptocurrencies, these crypto transactions are also secure messages only, which gives the private key owner the right to decrypt the message on that public key or in other words the right to spend those cryptocoins present on that public key (address).
Difference Between Public Key And Private Key Cryptography In A Tabular Form
| Private Key Cryptography | Public Key Cryptography |
| It is one key system based on the private key | It is a two-key system based on private and public keys |
| The private key must be kept secret | One of the two keys must be private. Generally, the public key can be shared. |
| Easy encryptions with easy to guess or brute force passphrases can be deciphered | Easy encryptions with easy to guess or brute force passphrases can be deciphered |
| The sender and receiver must share the algorithm and the key. | The sender and receiver must each have one of the linked pairs of keys. |
| Encryption of this form takes less time | Encryption of this form takes more time |
So that’s all from my side in this article of public and private keys.
Now you tell us: What do you think about these two branches of cryptography? Which form of encryption should be used and why? Tell us your thoughts using the comments section below.
- Is Bitcoin Real Money?: Understanding Different Types Of Money - June 28, 2024
- Bitcoin Transaction Accelerator: 5 Services to Unstuck Your BTC - September 23, 2023
- What Is Bitcoin Private Key? Everything You Need To Know !! - June 2, 2023